Your Business Is Protected Even When You’re Not Watching
24/7 human-powered monitoring that detects and stops threats in real time, before they turn into downtime, financial loss, or disruption. Watch this short video to see what actually happens when a cyber threat hits at 2:07 a.m. and how it gets stopped before your team even logs in.
Why This Matters for Your Business
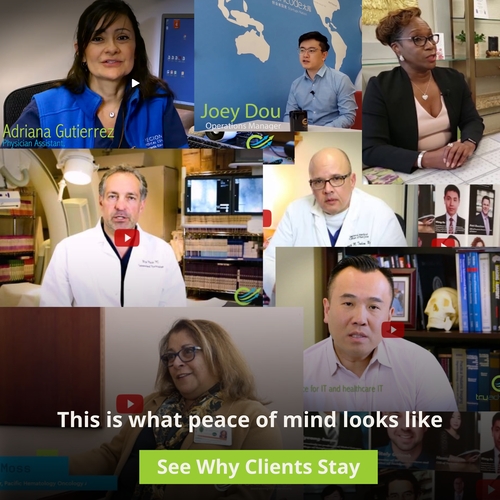
Peace of Mind
You don’t have to worry about what’s happening after hours. Your environment is continuously monitored and actively protected.
Reduced Downtime
Threats are contained early, often before employees even notice an issue.
Lower Financial Risk
Stops ransomware, wire fraud, and breaches before they turn into costly incidents.
No Burden on Your Team
Security decisions and actions are handled in real time by experts, not your internal staff.
What This Looks Like in Real Life

Incident
A login attempt appeared from another country just minutes after a U.S.-based login.
What Happened
This is what’s known as an “impossible login,” a strong indicator that credentials may have been compromised.
What We Did
- Detected the anomaly instantly
- Disabled the account within seconds
- Contained the threat before access was gained
Business Impact
No breach, no escalation, no disruption to the business.

Incident
An employee clicked what looked like a normal invoice.
What Happened
Ransomware behavior began, specifically abnormal file encryption that typically spreads across shared systems and servers.
What We Did
- Detected unusual encryption activity immediately
- Isolated the device within seconds
- Prevented the spread across the network
Business Impact
One laptop was cleaned instead of the entire business being shut down for days.

Incident
An employee received an email that appeared to come from their CEO requesting an urgent wire transfer.
What Happened
This was a business email compromise attempt, designed to create urgency and bypass normal verification processes.
What We Did
- Identified the signs of impersonation
- Blocked the message before it reached the inbox
- Alerted the team proactively
Business Impact
A six-figure financial mistake was avoided with zero disruption.
What Our 24/7 Security Operations Center Does for Your Business
Most security tools send alerts.
Our SOC takes action.
- Detects and responds in seconds
Suspicious activity is identified and contained immediately, not after damage is done - Stops ransomware before it spreads
Infected devices are isolated instantly to protect the rest of your environment - Blocks phishing and wire fraud attempts
Prevents costly mistakes before they reach your team - Monitors Microsoft 365 and user activity
Protects logins, access behavior, and account security - Covers endpoints, email, and network together
Full visibility across your entire environment, not siloed tools - Included from day one
No upsells, no add-ons, this level of protection is standard
Most IT Providers Alert You. We Act.
Many providers rely on alerts and tickets.
Our approach is different: We detect, respond, and contain threats immediately, then keep you informed. Because in cybersecurity, minutes matter.
See What This Looks Like for Your Environment
If you’re not sure what’s being monitored today or how quickly threats are being handled, it’s worth taking a look.